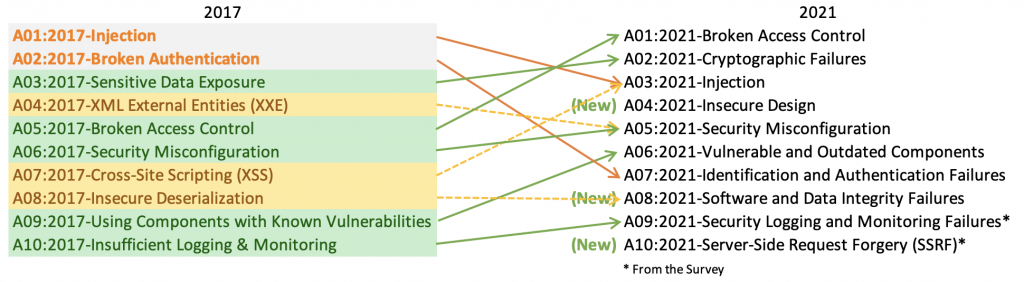
We got a new version of the OWASP top 10 vulnerabilities from OWASP. It still in draft version. Nevertheless we can already see where the security world is shifting to. In this article we will go through the different vulnerabilities from the 2021 top 10 as well as compare against the 2017 standard.

If we have to summarize all the changes in one paragraph this would be it. We have three new categories. Some of the old categories disappear, this is mostly because this get grouped in other categories that change scope.
The new categories are: Insecure Design, Software and Data Integrity Failures and Server-Side Request Forgery(SSRF). Software and Data Integrity failures includes Insecure Deserialization which is A08:2017. This was found in several libraries shared among developers.
In this section, we are going to analyze the 2021 Top10 vulnerabilities:
A01: Broken Access Control: Access control is the one that ensures that users only access the data that they are authorized to use. Usually, failures in this system allow the user to access unauthorized resources. Examples of broken access control may allow users to access resources by entering resource URLs, changing cookie parameters, or using another user ID to make the requests.
A02: Cryptographic failures: This can involve using insecure protocols like HTTP, SMTP, or FTP. Another common cause of failure is the use of old broken encryptions like MD5. Also, optional encryption can lead to data leaks; any time that data travels between client and server, this should be encrypted. Some good practices are classifying data to identify sensitive data. Apply controls and ensure sensitive data is not stored or transmitted unless necessary, and this is done securely.
A03:Injection: Usual failures of this kind are due to a lack of data validation and sanitation. This category merges the A01-2017: Injection and the A07-2017 Cross-site scripting(XSS), which is another injection based on passing pieces of code(scripts) as variables. One of the best practices to avoid injection attacks is to keep data input separated from commands and queries. Use positive server-side input validation. Another good practice is to use the LIMIT and other SQL controls to prevent mass disclosure o records in SQL injection.
A04:Insecure Design: This category is vast. It can include the lack of controls and validation, lack of encryption… Some of the best practices to mitigate this vulnerability are: Establish a secure development lifecycle with Subject matter experts. Establish and use a library of secure designs or pieces that are secured by design. Use thread modeling for the different flows.
A05:Security Misconfiguration: This category is also extensive; it can include missing security hardening controls, improper permissions configurations in the cloud or even the installation of unnecessary features, opening unnecessary ports or services. Some of the best practices to mitigate security misconfigurations are: Create a minimal platform, avoiding unnecessary features, components, and even documentation. Also, segment the application architecture or provide separation between components or tenants.
A06: Vulnerable and Outdated Components: This vulnerability is relatively self-explanatory. To prevent to suffer from vulnerable and outdated components, we should remove unused dependencies and unnecessary features. Continuously inventory the versions for libraries and components that we use(including OS).
A07:Identification and Authentication Failures: This can include leaving default passwords, setting simple passwords, avoid showing session ID’s and ensure proper configuration of MFA. Best practices include not deploying applications with default credentials, implementing MFA when possible, ensuring registration and credential recovery, and aligning password complexity with NIST 800-63b.
A08:Software and Data Integrity Failures: This relates to code and infrastructure that does not ensure integrity. This can be from a cookie stored in plain text that the attacker can use for privilege escalation or a misconfiguration in the CDN or third-party repositories with vulnerabilities. Best practices recommend verifying data and software via digital signature or similar to ensure sound sources. Also, it is recommended to use repository managers like npm or Maven, which are trusted and ensure their libraries’ security.
A09:Security logging and monitoring: It is usually a forgotten practice to log and monitor events and status once the application or service reaches production. This can generate a slow response time that can be critical when responding to incidents. Best practices recommend logging all access control and server-side input validation failures with enough context to identify suspicious or malicious accounts. These logs should be formatted so that log management solutions can easily consume (We can get more info in the NIST 800-92).
A10: Server Side request forgery (SSRF): This refers to the event of illegitimate users sending requests to resources that shouldn’t be accessible for the user. This usually happens due to a lack of URL validation on the server side. To mitigate this kind of attack, we can add measures in two different OSI layers; from the network layer, we can segment remote resources to reduce the impact of a successful attack and enforce a “deny by default” policy in FW and ACL rules. We can sanitize and validate all client-supplied content from the application layer, enforce a URL schema and port into a positive allow list, avoid sending unencrypted responses, and disable HTTP redirections.
To summarize all the changes, we can say that none of the old TOP10 attacks has disappeared. Nevertheless, they have evolved, and now we are seeing new kinds of attacks showing up thanks to automation tasks and easier access to easy-to-use but powerful applications.
Cybersecurity should always be a concern to every entity that has a presence in cyber-space. This includes people as well as corporations. On the other hand, as attacks evolve, security measures, next-generation firewalls, web application firewalls, and different tools for intrusion detection and prevention mechanisms are also widely spread. And with the introduction of ML and IA to those products, we are better protected every day!